Choosing the Right Identity Provider A Checklist for CIOs & CISOs
Topic : information technology | other
Cybercriminals aren’t slowing down — and neither should you. From account takeovers and insider threats to partner access risks, modern enterprises need an identity-first approach to protect every user, device, and transaction.
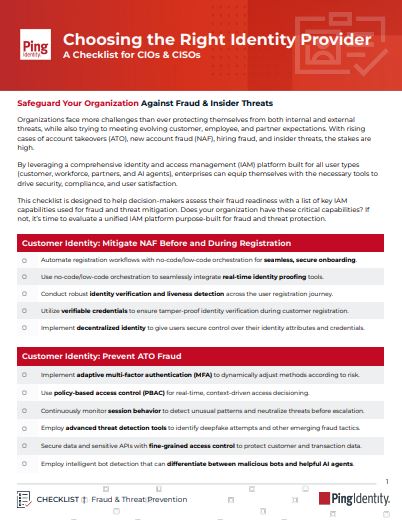
The Choosing the Right Identity Provider: A Checklist for CIOs & CISOs gives you the essential fraud and threat prevention capabilities to:
- Stop account takeover (ATO) and new account fraud (NAF) with adaptive MFA and advanced threat detection.
- Verify identities securely at registration with liveness detection and verifiable credentials.
- Build customer trust with passwordless authentication and secure loyalty program integrations.
- Enforce Zero Trust and least-privilege access for workforce and AI agents.
- Control third-party access with real-time visibility and policy-based access control.
- Speed deployment with a unified, low-code/no-code IAM platform.
With a focus on customer, workforce, and partner identity security, this checklist helps leaders quickly assess their gaps and implement the right capabilities for a safer, more compliant organization.
Download now to strengthen your fraud defense strategy and choose an identity provider built for today’s threats.
Want to learn more?
Submit the form below to Access the Resource